WordPress API wp_remote_get and wp_remote_post may use cURL as the underlying technology. cURL doesn’t have an in-built certificate, like all the browsers and relies on external certificates to verify SSL of websites. In majority of setups things just work fine and you don’t need to worry much about it.
Certificate Authority is the top certificate which is provided by Certification Authority firms. We can provide another certificate authority like our company local certificate authority with the -cacert option. $ curl -cacert mycompany.cert https://www.mycompany.com.

- Marketing cookies are used to track visitors across websites. The intention is to display ads that are relevant and engaging for the individual user and thereby more valuable for publishers and third party advertisers.
- Curl is using the system-default CA bundle is stored in /etc/pki/tls/certs/ca-bundle.crt. Before you change it, make a copy of that file so that you can restore the system default if you need to. You can simply append new CA certificates to that file, or you can replace the entire bundle. Are you also wondering where to get the certificates?
- The PEM file allows cURL to connect securely to the Zendesk API using the Secure Sockets Layer (SSL) protocol. Move the cacert.pem file to your C: curl folder and rename it curl-ca-bundle.crt. Add the curl folder path to your Windows PATH environment variable so that the curl command is available from any location at the command prompt.
But in some cases, connecting to websites over https fails because of missing or incorrect cURL. In this regard, we need to point PHP cURL to use the correct one.
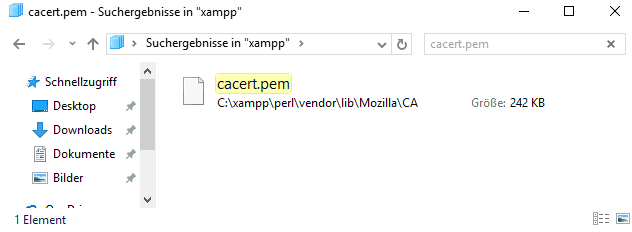
Download the updated current cacert.pem file from cURL website. Place it somewhere in your system.
Now edit your php.ini file. If you are on a dedicated or VPS server, then you know which file to edit (or your sysadmin knows). If on a shared server, then I highly recommend to get help from your webhost support. If you are feeling geeky, then use this guide to find out how to locate your php.ini file.
Now place/modify the following directive.
You can store the files anywhere and refer to the absolute path. Once done, save the ini file and restart the server.
For Nginx
For Apache
When you use curl to communicate with a HTTPS site (or any other protocol that uses TLS), it will by default verify that the server is signed by a trusted Certificate Authority (CA). It does this by checking the CA bundle it was built to use, or instructed to use with the –cacert command line option.
Curl Cacert Example
Sometimes you end up in a situation where you don’t have the necessary CA cert in your bundle. It could then look something like this:
Do not disable!
A first gut reaction could be to disable the certificate check. Don’t do that. You’ll just make that end up in production or get copied by someone else and then you’ll spread the insecure use to other places and eventually cause a security problem.
Get the CA cert
I’ll show you four different ways to fix this.
1. Update your OS CA store
Operating systems come with a CA bundle of their own and on most of them, curl is setup to use the system CA store. A system update often makes curl work again.
This of course doesn’t help you if you have a self-signed certificate or otherwise use a CA that your operating system doesn’t have in its trust store.
2. Get an updated CA bundle from us
curl can be told to use a separate stand-alone file as CA store, and conveniently enough curl provides an updated one on the curl web site. That one is automatically converted from the one Mozilla provides for Firefox, updated daily. It also provides a little backlog so the ten most recent CA stores are available.
If you agree to trust the same CAs that Firefox trusts. This is a good choice.
3. Get it with openssl
Now we’re approaching the less good options. It’s way better to get the CA certificates via other means than from the actual site you’re trying to connect to!
This method uses the openssl command line tool. The servername option used below is there to set the SNI field, which often is necessary to tell the server which actual site’s certificate you want.
A real world example, getting the certs for daniel.haxx.se and then getting the main page with curl using them:
4. Get it with Firefox
Suppose you’re browsing the site already fine with Firefox. Then you can do inspect it using the browser and export to use with curl.
Step 1 – click the i in the circle on the left of the URL in the address bar of your browser.
Step 2 – click the right arrow on the right side in the drop-down window that appeared.
Step 3 – new contents appeared, now click the “More Information” at the bottom, which pops up a new separate window…
Step 4 – Here you get security information from Firefox about the site you’re visiting. Click the “View Certificate” button on the right. It pops up yet another separate window.
Curl With Cert
Step 5 – in this window full of certificate information, select the “Details” tab…
Step 6 – when switched to the details tab, there’s the certificate hierarchy shown at the top and we select the top choice there. This list will of course look different for different sites
Step 7 – now click the “Export” tab at the bottom left and save the file (that uses a .crt extension) somewhere suitable.

If you for example saved the exported certificate using in /tmp, you could then use curl with that saved certificate something like this:
But I’m not using openssl!
This description assumes you’re using a curl that uses a CA bundle in the PEM format, which not all do – in particular not the ones built with NSS, Schannel (native Windows) or Secure Transport (native macOS and iOS) don’t.
If you use one of those, you need to then add additional command to import the PEM formatted cert into the particular CA store of yours.
A CA store is many PEM files concatenated
Curl Https Certificate
Just concatenate many different PEM files into a single file to create a CA store with multiple certificates.
